In crypto, self-custody is often treated like the final answer.
The argument is familiar: not your keys, not your coins. Take control, remove middlemen, and protect yourself from frozen accounts, exchange failures, hacks, platform restrictions, and custodial risk.
That argument is valid. Self-custody solves real problems. It is one of the reasons crypto exists in the first place: a person can hold value directly, without asking a bank, broker, exchange, payment company, or government-controlled account for permission.
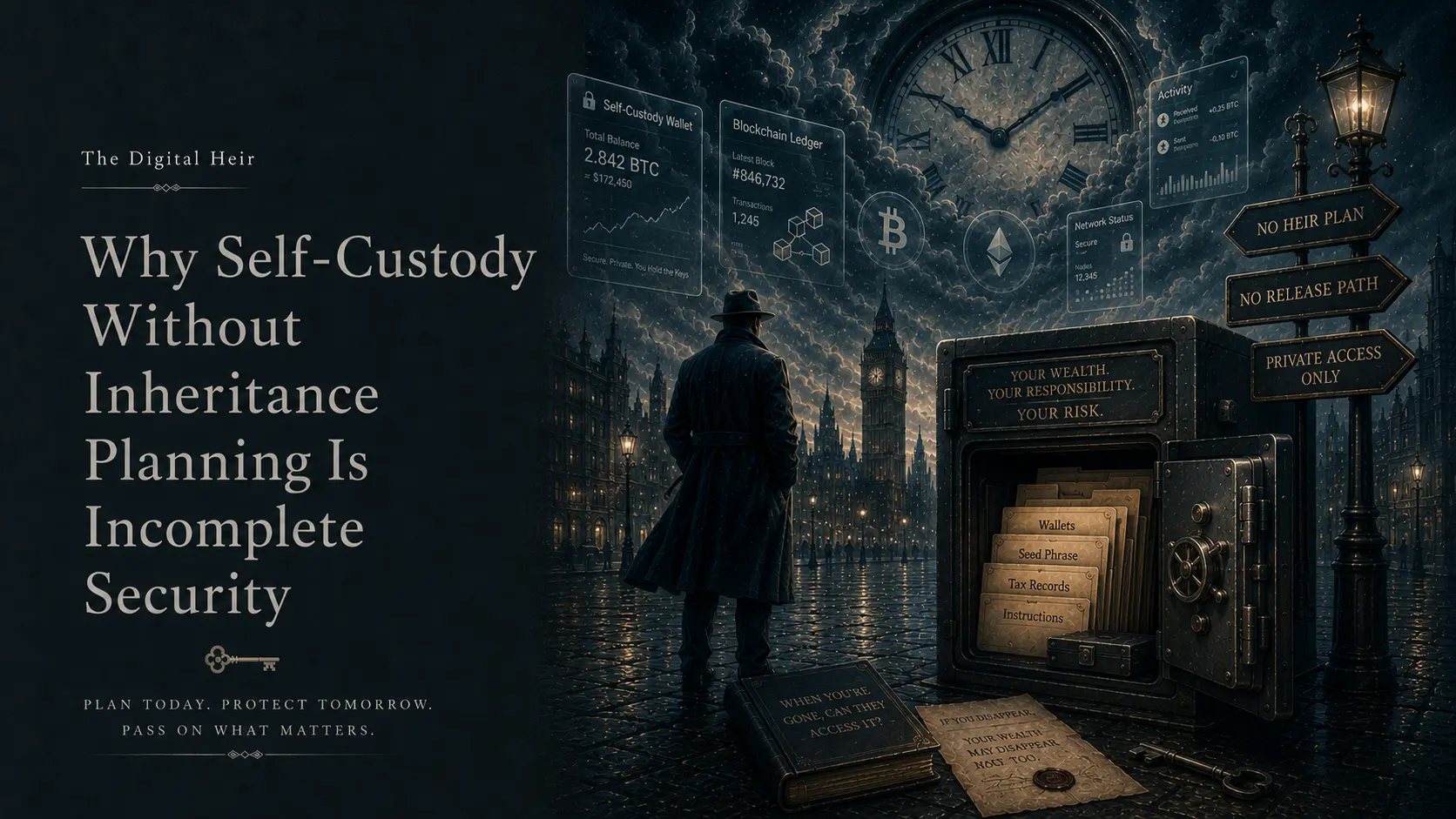
But self-custody also creates a quieter risk. It works beautifully right up until the moment the owner is no longer available: a sudden accident, a disappearance, a medical emergency, an unexpected death, a destroyed phone, a missing passphrase, a hardware wallet nobody recognizes, or a seed phrase that still exists somewhere, but not in a place anyone knows how to find.
At that point, “secure” and “lost forever” start looking dangerously similar.
That is why self-custody without inheritance planning is incomplete security.
Self-custody protects against platforms, not against absence
Most self-custody conversations focus on external threats. An exchange can freeze withdrawals. A platform can collapse. A custodian can be hacked. A bank can block a transfer. A government can change the rules. A third party can decide that access to your own money is no longer convenient for them.
Self-custody reduces those risks by moving control back to the owner. But that control does not end with buying a hardware wallet or writing down a seed phrase. It also includes the question many people avoid: what happens if the owner is no longer here to explain the system?
Traditional assets usually leave traces. A bank account can often be found. A brokerage account may have beneficiary procedures. Real estate has public records. Insurance policies and pension accounts may have institutional processes around death and inheritance.
Self-custodied crypto can be different. It may leave behind a device, a metal plate, a piece of paper, or a private key that nobody understands. The blockchain may still show the coins, but the blockchain does not care who the heirs are. It only recognizes the key.
Lost crypto is already part of Bitcoin’s history
This is not a theoretical issue.
Ledger’s article, “How Many Bitcoin Are Lost?”, notes that analysts estimated in early 2025 that between 2.3 million and 3.7 million BTC may be permanently lost, representing roughly 11–18% of Bitcoin’s fixed maximum supply. Some reports suggest losses could be as high as 4 million BTC.
Nobody can know the exact number. An inactive wallet is not always a lost wallet. Some owners are long-term holders. Some coins may still be recoverable. Some wallets may simply not have moved for years.
But the broader point is hard to ignore: crypto can become economically dead even when it still exists on-chain. A private key can be forgotten, a hard drive can be thrown away, a hardware wallet can be destroyed, a passphrase can die with the owner, and a family can know there was crypto somewhere and still be unable to reach it.
That is not a hack, confiscation, or market crash. It is failed succession.
The inheritance trap inside self-custody
Self-custody has a strange weakness: the better you are at hiding access from everyone else, the easier it is to hide it from the people who may one day need it.
A seed phrase in a drawer may protect against a hacker. It does not automatically protect against fire, flood, theft, legal delay, family confusion, memory loss, or the simple fact that nobody else knows what the words mean.
A metal backup may survive physical damage. It does not explain which wallet to use, whether there is an additional passphrase, which networks hold assets, or whether funds are split across multiple chains.
A hardware wallet may be safe from malware. It does not explain the PIN, the signing process, the tax history, or who should help the heir avoid scams.
A multisig setup may reduce theft risk. It can also become a puzzle if nobody knows who the signers are, what the threshold is, or how to reconstruct the wallet.
This is the uncomfortable truth: security is not complete if it only works while the owner is alive, healthy, and available. A complete plan protects assets from attackers today and makes them recoverable by the right person tomorrow.
Self-custody without inheritance planning only solves the first half.
Revealing access too early creates its own danger
The obvious answer sounds simple: tell your heir.
But that is not always safe. If you tell someone that a large crypto inheritance exists, privacy is partly gone. Depending on the amount, the relationship, the country, and the family situation, that knowledge can create pressure, conflict, manipulation, or even criminal risk.
If you give access too early, you may lose control before you intended. Giving a seed phrase to a relative today means trusting not only that person, but also their devices, their spouse, their email account, their future financial stress, their ability to avoid phishing, and their judgment under pressure.
Even a good person can make a bad mistake. They can store the phrase in cloud notes, show it to someone “technical,” type it into a fake recovery website, move funds on the wrong network, or accidentally reveal that the assets exist to someone who should never know.
So the inheritance problem is not solved by exposing everything early. That may only replace one risk with another.
Revealing nothing can be worse
The opposite approach is total secrecy: tell nobody, hide everything, and trust only yourself.
That may feel safer while life is normal, but it creates another failure mode. If nobody knows the assets exist, nobody can inherit them. If nobody knows where the instructions are, nobody can follow them. If nobody knows who can help, the family may start searching online during a crisis. If nobody knows what not to do, they may expose the seed phrase to the first fake “wallet recovery” service they find.
This is how self-custody turns into accidental burning — not because the owner was careless with hackers, but because the owner was too careful to leave a usable path.
A complete plan has to avoid both extremes. It should not expose the secret too early, but it also should not leave the secret impossible to recover later.
The hard question is not only where to store the information. The hard question is when it should be released.
The missing layer is conditional release
Most inheritance tools were designed for a cleaner world than the one people actually live in. A will usually works after death. A lawyer can hold documents. A safe can hold paper backups. A password manager can store secrets.
But crypto inheritance often needs something more precise: conditional release.
Too early is dangerous. Too late is useless. Never is permanent loss.
A practical crypto inheritance process should answer several questions. What signs suggest the owner is unavailable? Which contact channels should be checked? How long should the system wait? Who should be notified? What information should be released first? How long should an access link remain valid? What should the heir do before touching the assets?
This is the part simple backup strategies usually miss. A paper seed phrase stores a secret, but it does not decide when that secret should be released. It does not check whether the owner is alive, missing, incapacitated, detained, or simply offline. It does not guide the heir, protect against family chaos, or connect the legal world with the technical world.
Crypto inheritance is not just storage. It is controlled delivery.
Exchanges do not remove the inheritance problem
This issue is not limited to pure self-custody.
Keeping funds on a crypto exchange may simplify some parts of inheritance, but it does not make the problem disappear. A legal heir may still need death certificates, identity documents, probate papers, court documents, exchange-specific procedures, and time.
The exchange may freeze the account while reviewing the case. The heir may not know the account exists. The owner may not have kept records. Two-factor authentication may be tied to a lost phone or email. The exchange may operate under rules that do not match the family’s expectations.
There is also a harder issue: personal intention and local inheritance law do not always match. Some people want to leave assets to a specific person, partner, friend, sibling, or child — not necessarily according to the default rules in their jurisdiction. In some countries, forced-heirship rules may limit what a person can do. A private instruction cannot simply override the law everywhere.
But from a practical planning perspective, crypto still creates a special question: how will the right person receive the information needed to act?
The custody model changes the problem. It does not remove the need for planning.
A real plan needs more than a seed phrase
A serious crypto inheritance plan should answer four basic questions.
First: what exists? Your heir does not necessarily need live balances today, but there should be a way to discover the assets after something happens. That may include wallet types, exchanges, chains, hardware wallet locations, tax-record locations, and trusted contacts.
Second: who is allowed to act? Legal authority matters. A will, trust, estate document, or local legal process may still be necessary. A technical access path does not replace estate planning.
Third: how can access happen safely? The heir may need instructions, not just secrets. They need to know what not to click, who not to trust, which wallet software to use, when to get professional help, and what should happen before any transaction is made.
Fourth: when should the information be released? This is the key inheritance problem. If the answer is “immediately,” the plan may be unsafe. If the answer is “only if someone finds a drawer,” the plan may be useless.
Inheritance planning for crypto is not just about possession. It is about timing, context, authority, and safe execution.
Where The Digital Heir fits
This is the gap The Digital Heir is designed to address: not as a replacement for a will, a lawyer, or tax planning, but as a conditional delivery layer for sensitive recovery information.
The Digital Heir is a live open-source service for secure digital inheritance. It is designed to pass critical information to the right person only if the owner becomes unavailable, without exposing that information too early.
The basic idea is simple. You create an encrypted Envelope directly in your browser, choose your Digital Heir, define human-memorable secret questions that your heir should be able to answer, and set a custom inactivity Pipeline using contacts such as Telegram, email, and WhatsApp.
If the Pipeline reaches its end, your Heir receives a limited-time path to try to unlock the Envelope.
That Envelope can contain practical recovery instructions: where a hardware wallet is stored, which wallets or exchanges exist, which lawyer or technical helper to contact, where tax records are located, what not to do with a seed phrase, and what steps should happen before any transaction.
The important point is not only encryption. It is timing.
Your heir does not need access while everything is fine. But if you become unavailable, there is a structured path for the information to reach the right person.
That is exactly where many crypto inheritance plans break.
The uncomfortable question
If you self-custody crypto, the question is not only whether your coins are safe from hackers. The better question is whether the right person can recover them if you are no longer here to explain anything.
If the answer is no, the setup is incomplete.
You may have removed the exchange. You may have protected yourself from platform failure. You may have a hardware wallet, a metal backup, and a careful storage routine. You may have done everything the self-custody community recommends.
But if your death, disappearance, or incapacity makes the assets unreachable, then the security model still has a hole in it.
Self-custody is control. Inheritance planning is continuity.
Without continuity, control can die with the owner.
And in crypto, when access dies, the assets often die with it.